How a Security Team use Policy as Code for Open Source Security
Table of Contents
SBOM is being mandated in certain regulated industries, especially for tracking open source dependencies. However the usefulness of SBOM, which is basically an inventory, is the tooling and use-cases around it. Conventional SCA tools are notorious for false positives and noise. Ability to prevent insecure or risky open source components proactively is required to maintain a healthy and trustworthy open source software supply chain. In this talk, we look at how to use vet for establishing security guardrails against risky OSS components. We also look at a case study of how a security team leverage vet's policy as code feature for enforcing opinionated security policies.
- vet
- sbom
- sql
- cloud
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
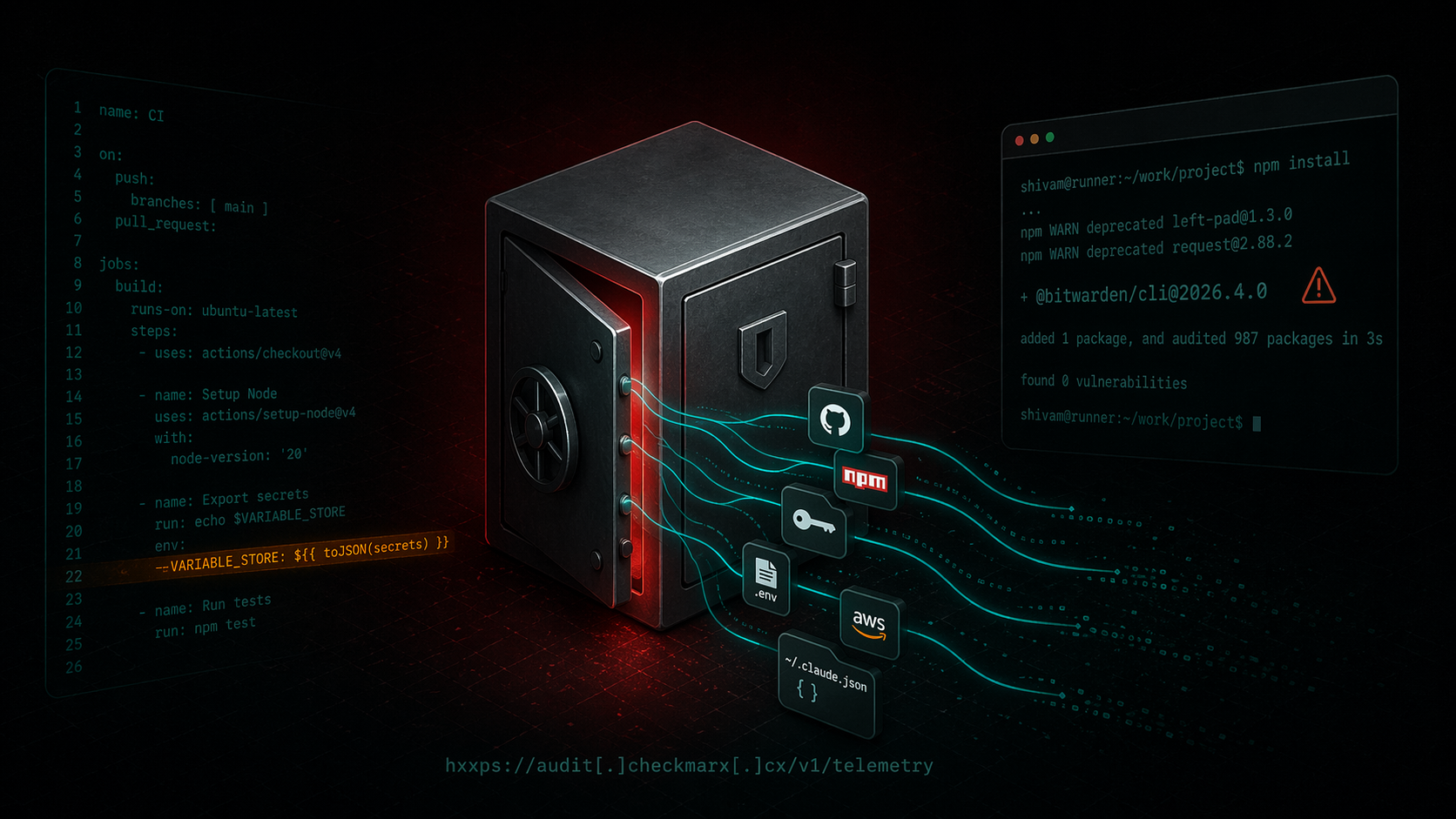
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/cli@2026.4.0` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...

ixpresso-core: Windows RAT Disguised as a WhatsApp Agent
ixpresso-core poses as an AI WhatsApp agent on npm but installs Veltrix, a Windows RAT that steals browser credentials, Discord tokens, and keystrokes via a hardcoded Discord webhook.
Malicious Pull Requests: A Threat Model
A compact threat model of the malicious pull request as a supply chain attack primitive against GitHub Actions: attacker, goals, assets, controllable surface, and an attack vector taxonomy (V1...
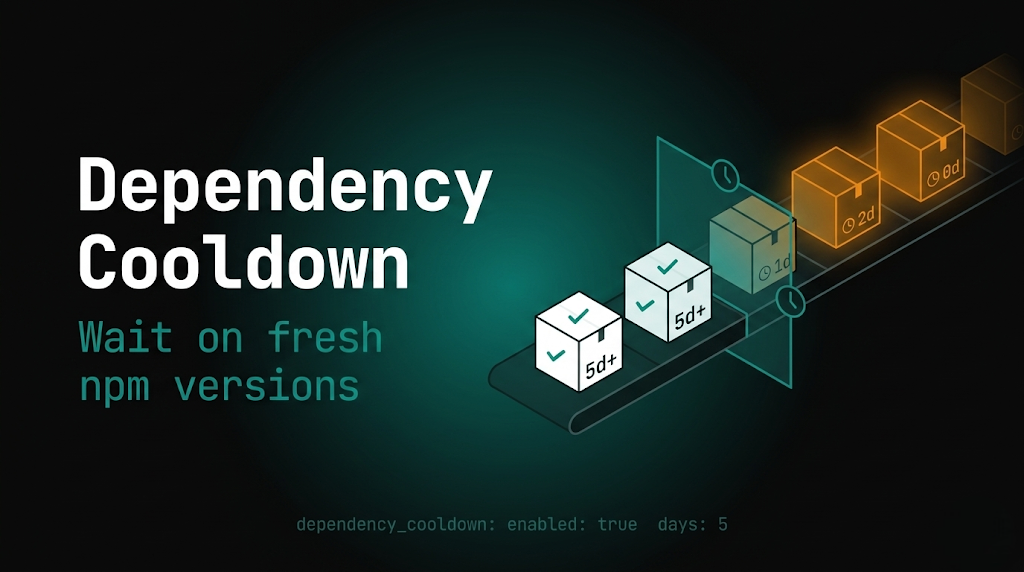
PMG dependency cooldown: wait on fresh npm versions
Package Manager Guard (PMG) blocks malicious installs and now supports dependency cooldown, a configurable window that hides brand-new npm versions during resolution so installs prefer older,...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
