PMG dependency cooldown: wait on fresh npm versions
Table of Contents
PMG (Package Manager Guard) wraps npm, pnpm, pip, and other package managers so installs are checked against SafeDep threat intelligence and run in OS sandboxes before arbitrary install scripts touch your machine. For background, see Introducing Package Manager Guard (PMG).
Dependency cooldown is a separate control: it trims registry metadata so version resolution normally ignores releases that are too new. That reduces the window where a compromised or rushed publish is the only version a semver range can pick.
How cooldown works
When cooldown is on, PMG filters npm package metadata and drops versions published inside the configured window (for example, the last 5 days). If the range still matches an older release, the resolver uses it. If nothing outside the window satisfies the range, the install fails until you widen the range, wait, or bypass cooldown (see below).
Cooldown applies to metadata-driven resolution. It does not apply to flows that already use a fixed tarball URL (direct tarball installs, some lockfile or cache cases). See the upstream dependency cooldown notes for details.
Requirement: cooldown needs proxy mode enabled. It is npm-only in the current release.
Install and shell setup
brew install safedep/tap/pmgor:
npm install -g @safedep/pmgWire the shell once (restart the terminal after):
pmg setup installRe-run pmg setup install after upgrades so new options land in your environment.
Enable dependency cooldown
Configuration lives in config.yml (create it via pmg setup install if needed). Example:
dependency_cooldown: enabled: true days: 5Adjust days to your risk tolerance: longer windows mean more installs fall back to older versions; shorter windows allow newer releases sooner.
One-off install without changing the file:
pmg --skip-dependency-cooldown npm install expressDocs and source
- pmg
- npm
- supply-chain
- security
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
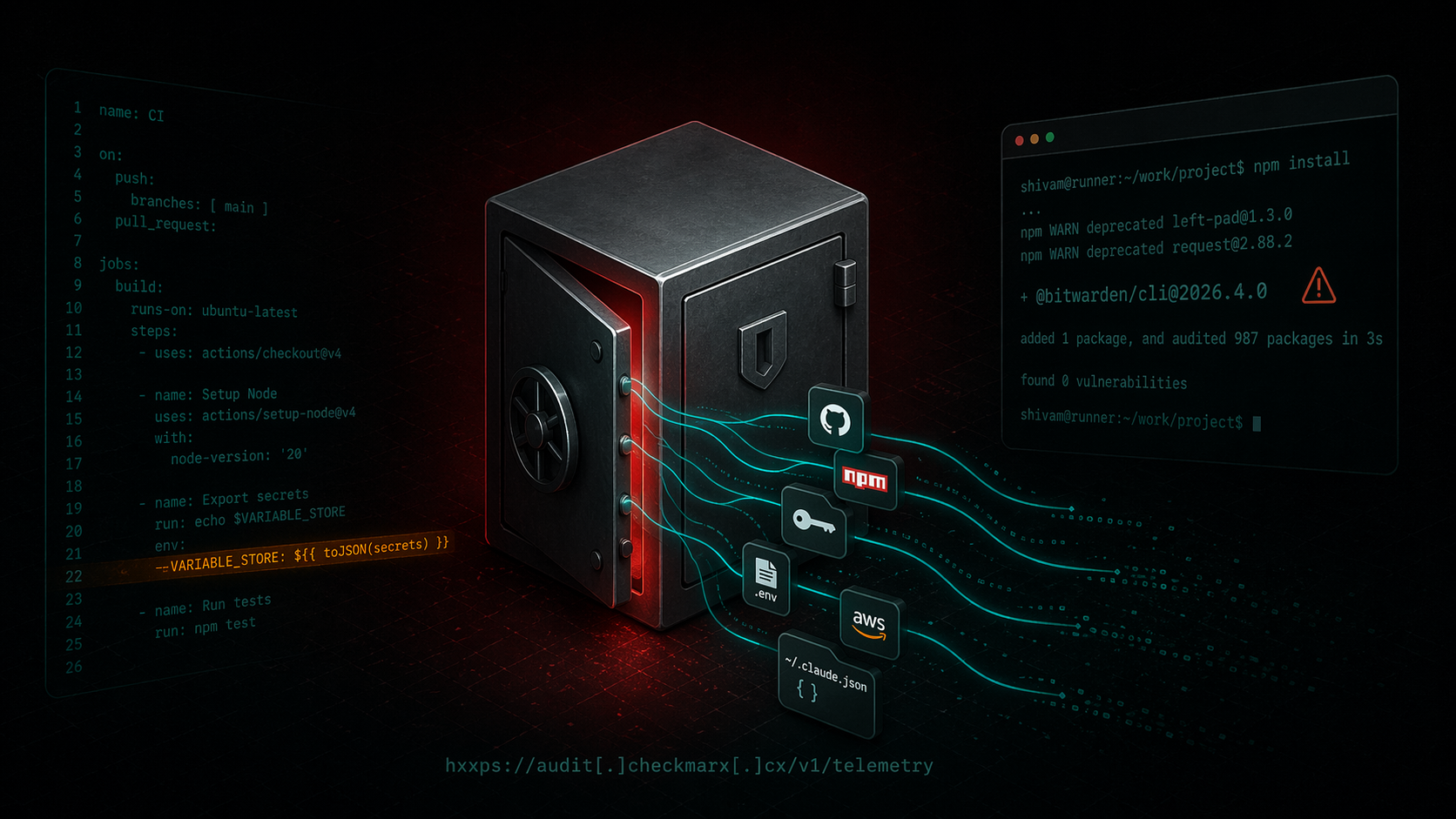
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/cli@2026.4.0` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...

ixpresso-core: Windows RAT Disguised as a WhatsApp Agent
ixpresso-core poses as an AI WhatsApp agent on npm but installs Veltrix, a Windows RAT that steals browser credentials, Discord tokens, and keystrokes via a hardcoded Discord webhook.
Malicious Pull Requests: A Threat Model
A compact threat model of the malicious pull request as a supply chain attack primitive against GitHub Actions: attacker, goals, assets, controllable surface, and an attack vector taxonomy (V1...

forge-jsx npm Package: Purpose-Built Multi-Platform RAT
forge-jsx poses as an Autodesk Forge SDK on npm. On install it deploys a system-wide keylogger, recursive .env file scanner, shell history exfiltrator, and a WebSocket-based remote filesystem...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
