Ship Code. Not Malware. SafeDep Launches GitHub App for Malicious Package Protection
Table of Contents
Malicious Package in the Wild
The recent supply chain attack targeting the npm ecosystem, such as the Shai-Hulud and the S1ngularity campaign, has raised serious concerns among the developer and security engineering community. Detecting malicious code in open source packages is a complex problem, and it requires a multi-layered approach. We have been doing this for a while leveraging:
While we handle the complexity, we have always strived to provide the simplest and minimally intrusive solution to protect developers from malicious packages. So we launched SafeDep GitHub App to make it ridiculously simple to protect your code repositories from malicious packages.
Installation is simple and zero configuration - Install Now
Zero Configuration Malicious Package Protection
How To Get Started?
- Install the SafeDep GitHub App
- Wait for the next pull request to be scanned
- Stay protected from malicious packages
That’s it! It is really that simple. Here is how it looks like in action:
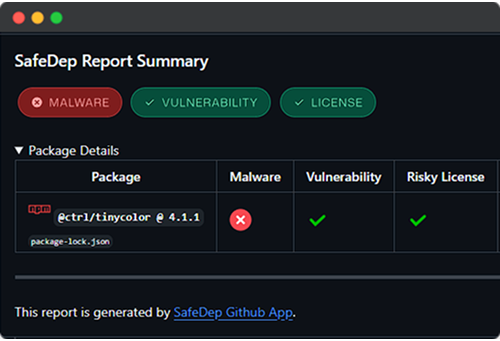
How it works?
SafeDep scans all open source packages released to supported registries such as npm, PyPI, RubyGems, Cargo and more. SafeDep applies static, dynamic and agentic analysis to detect malicious packages. While these packages are removed from the registries, SafeDep tools leverage this threat intelligence to protect code repositories from malicious packages.
What are the benefits?
- Zero Configuration: Install the app with zero configuration
- Real-time Protection: Scans every pull request for malicious packages
- Multi-Ecosystem: Supports npm, pnpm, yarn, and more
- Multi-Language: Supports JavaScript, TypeScript, Python, and more
- Multi-Platform: Supports Windows, Linux, and macOS
Documentation and Support
- GitHub App Documentation: SafeDep GitHub App
- Community support: https://docs.safedep.io/community
- npm
- oss
- malware
- supply-chain
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
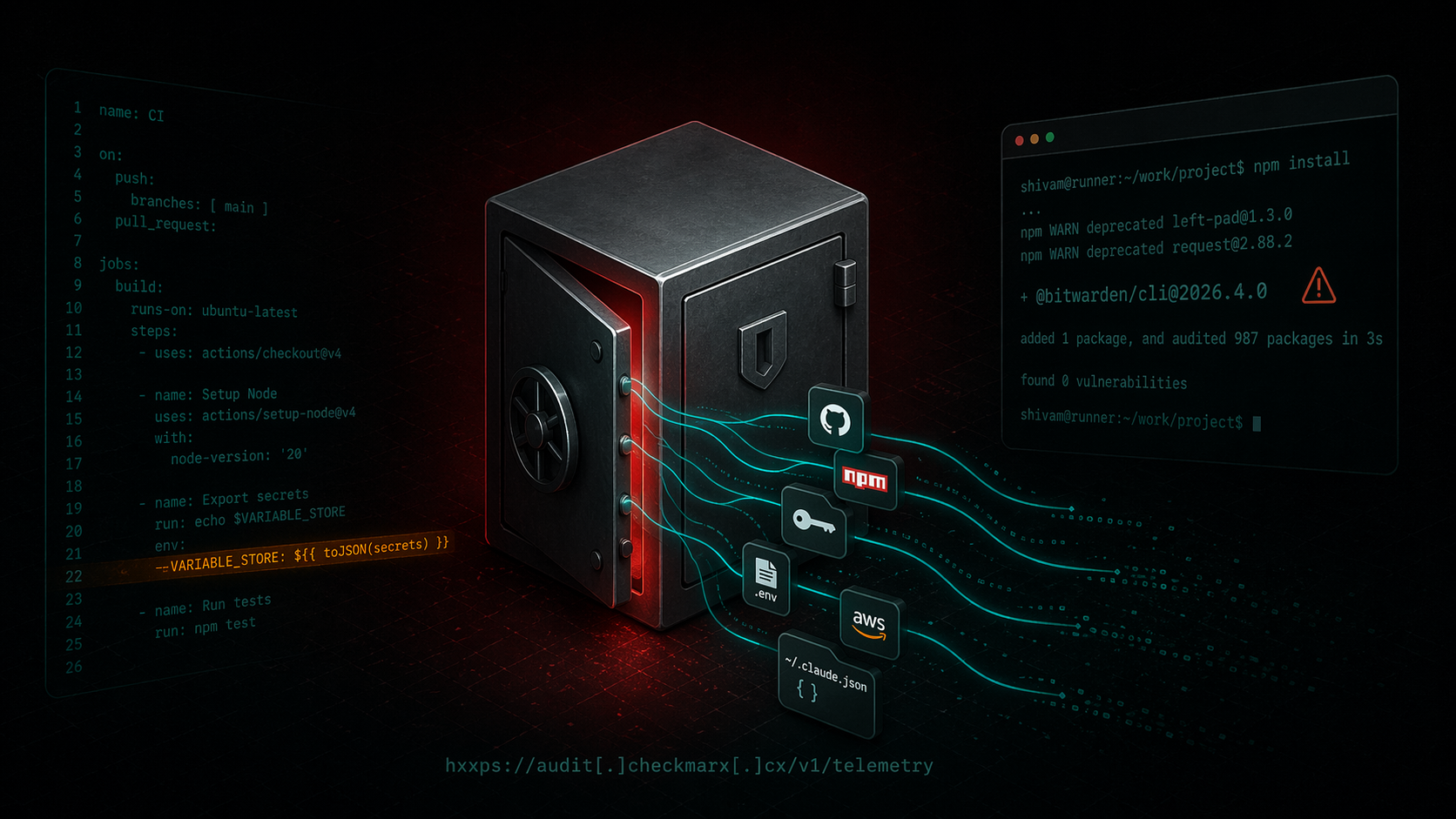
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/cli@2026.4.0` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...

ixpresso-core: Windows RAT Disguised as a WhatsApp Agent
ixpresso-core poses as an AI WhatsApp agent on npm but installs Veltrix, a Windows RAT that steals browser credentials, Discord tokens, and keystrokes via a hardcoded Discord webhook.
Malicious Pull Requests: A Threat Model
A compact threat model of the malicious pull request as a supply chain attack primitive against GitHub Actions: attacker, goals, assets, controllable surface, and an attack vector taxonomy (V1...
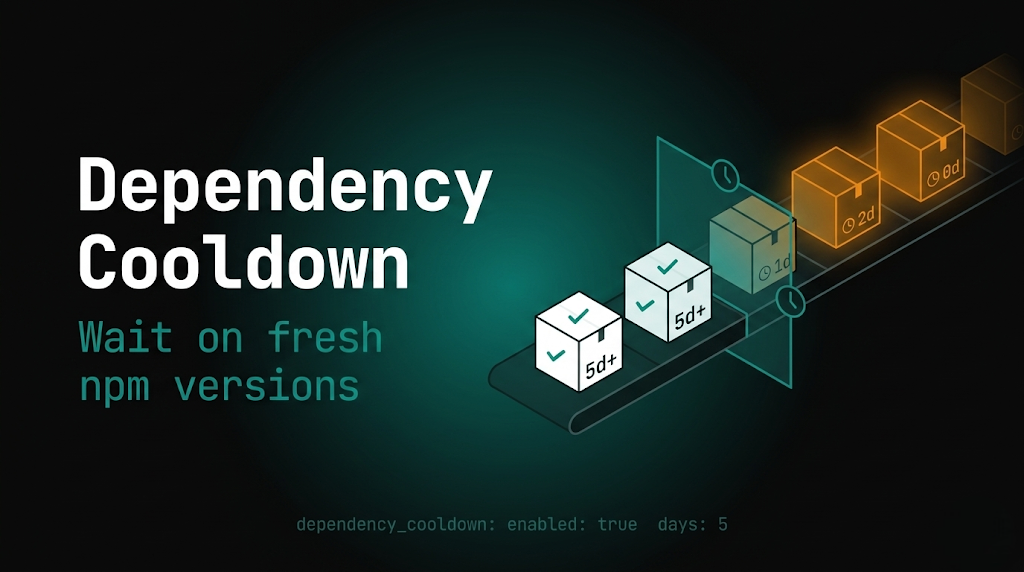
PMG dependency cooldown: wait on fresh npm versions
Package Manager Guard (PMG) blocks malicious installs and now supports dependency cooldown, a configurable window that hides brand-new npm versions during resolution so installs prefer older,...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
