Introducing Package Manager Guard (PMG)
Table of Contents
Let’s say you are building an Express.js application. You need a cookie parser middleware. But instead of installing the original cookie-parser package, you install express-cookie-parser which is a malicious package, although removed from the npm registry. We developers want to get the job done while in the flow state. We hate going outside our terminals and IDEs to check if a package we are installing is malicious or not. This behavior is exploited by malicious actors to compromise developers through typosquatting and other supply chain attacks. To protect the software supply chain, we need to protect developers from malicious packages at the time of installation. This is where Package Manager Guard (PMG) comes in.
What is PMG?
PMG is a tool to protect developers from malicious packages at the time of installation. It is a CLI tool that wraps popular package managers like npm, pnpm, etc. It prevents installation of malicious packages by scanning the package at the time of installation.
How do I use PMG?
The easiest way to install PMG is using homebrew. For other installation options, please refer to the PMG GitHub repository.
brew install safedep/tap/pmgIn your NPM project, you can now install any package using pmg as a security guard.
pmg npm install reactThe goal of PMG is to be as hidden and out of the way as possible while protecting developers from installing malicious packages. For a seamless experience, add PMG as an alias for your package manager.
alias npm="pmg npm"alias pnpm="pmg pnpm"That’s it! PMG will now protect you from installing malicious packages.
Demo
Bugs and Feedback
If you find any bugs or have any feedback, please file an issue on the PMG GitHub repository. You can also join SafeDep Community Discord to discuss PMG and other SafeDep products.
- pmg
- malware
- security
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
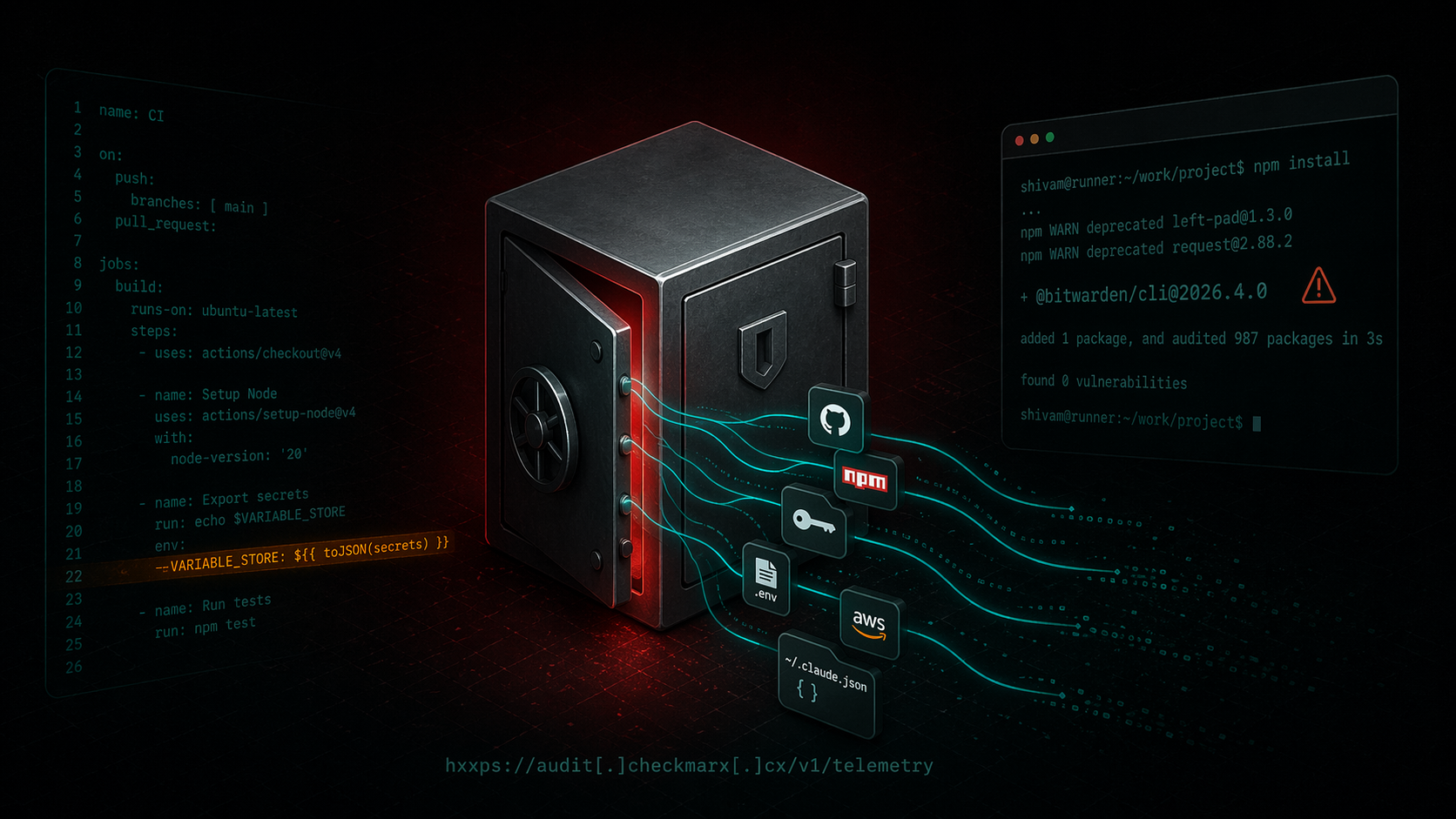
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/cli@2026.4.0` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...

ixpresso-core: Windows RAT Disguised as a WhatsApp Agent
ixpresso-core poses as an AI WhatsApp agent on npm but installs Veltrix, a Windows RAT that steals browser credentials, Discord tokens, and keystrokes via a hardcoded Discord webhook.
Malicious Pull Requests: A Threat Model
A compact threat model of the malicious pull request as a supply chain attack primitive against GitHub Actions: attacker, goals, assets, controllable surface, and an attack vector taxonomy (V1...
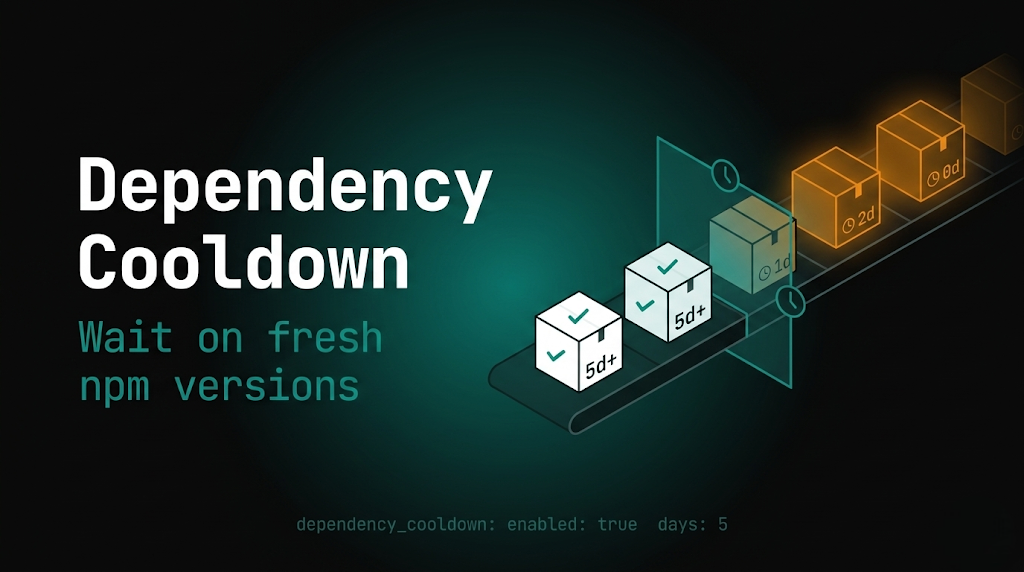
PMG dependency cooldown: wait on fresh npm versions
Package Manager Guard (PMG) blocks malicious installs and now supports dependency cooldown, a configurable window that hides brand-new npm versions during resolution so installs prefer older,...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
