Introducing vetpkg.dev - Open Source Component Security Dashboard
Table of Contents
Introducing vetpkg.dev
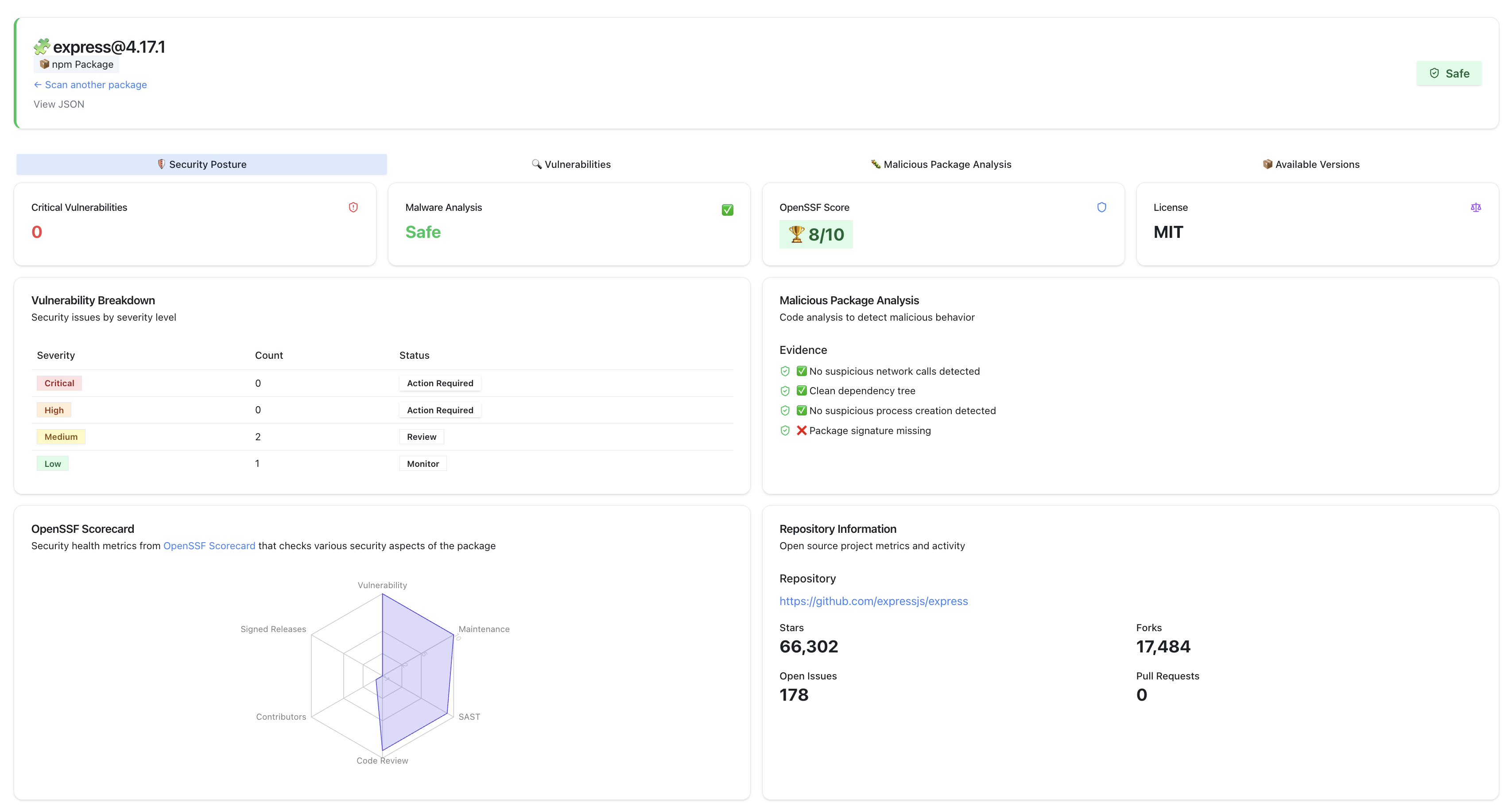
vetpkg.dev is a free service that provides visibility into the security of open source components. It is built using the SafeDep Cloud API to provide an easy to use interface for developers to check the security of their open source dependencies before using them in their projects.
Why did we build vetpkg.dev?
As the developers of vet, we often felt the need for customizing security metadata visualization for open source components. We wanted to mash up public and private data sources to provide easy access to aggregated security data. We expect that this information will help developers and security engineers make better decisions about the open source components before using them in their projects.
Using vetpkg.dev, we want to provide a simple and easy-to-use interface for having a single source of truth for open source component security information including malicious code analysis results.
How to use vetpkg.dev?
Using vetpkg.dev is simple. You can search for an open source component by its ecosystem, name and version. For example, navigate to the following URL
You can also search for specific component by navigating to vetpkg.dev
How does vetpkg.dev work?
vetpkg.dev uses the SafeDep Cloud API to fetch security information about open source components. This includes information about known vulnerabilities, licenses, project metadata, malicious code analysis results and more. It uses SafeDep Insights API to fetch the required information.
Example
The source of screenshot below is available here
- sca
- nextgen-sca
- reachability
- ossrisk
- guide
Author
SafeDep Team
safedep.io
Share
The Latest from SafeDep blogs
Follow for the latest updates and insights on open source security & engineering
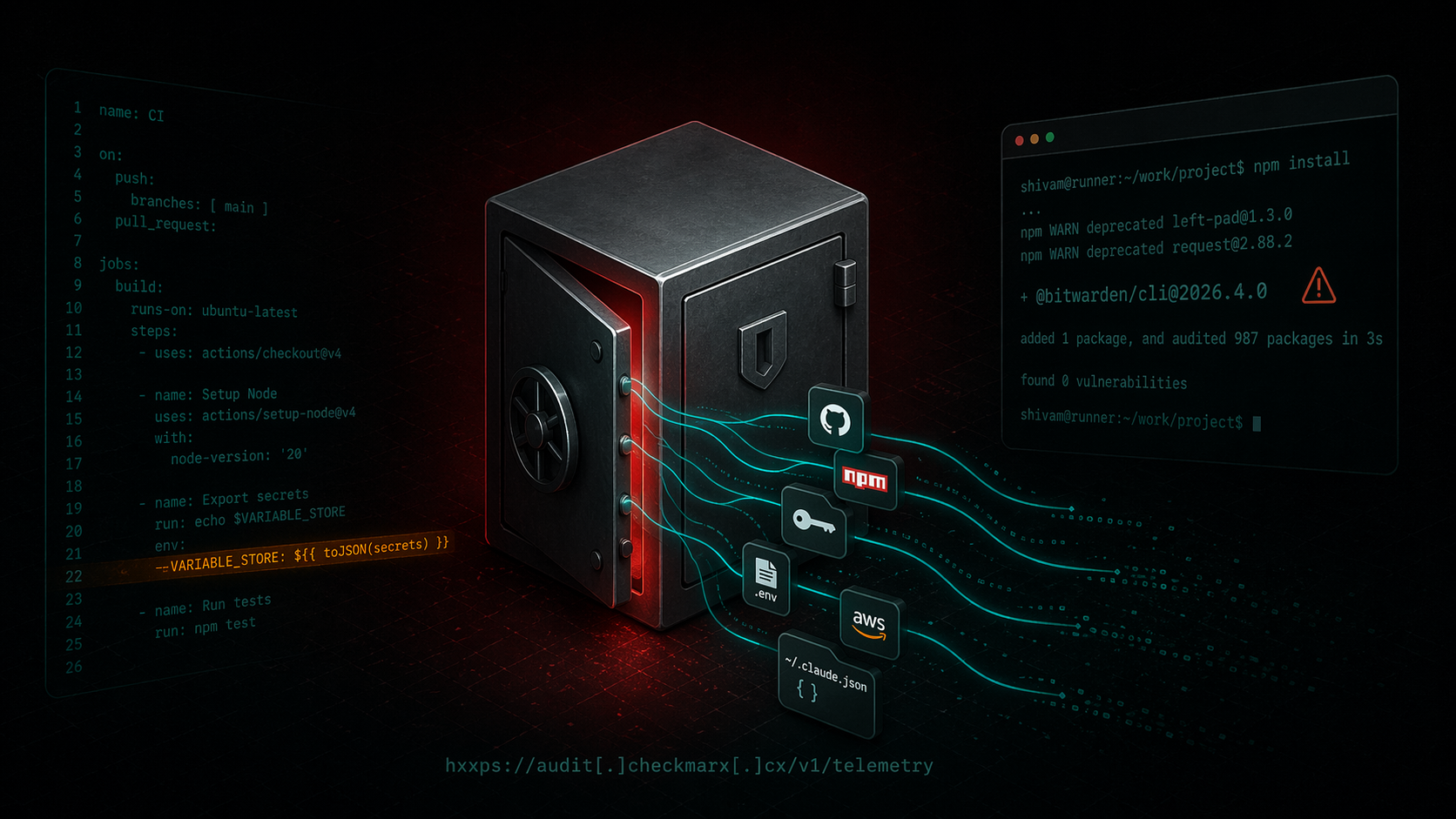
Bitwarden CLI Supply Chain Compromise
A technical writeup of the malicious `@bitwarden/cli@2026.4.0` release linked to the Checkmarx campaign. Covers the poisoned publish path, loader changes, credential theft, GitHub abuse, and...

ixpresso-core: Windows RAT Disguised as a WhatsApp Agent
ixpresso-core poses as an AI WhatsApp agent on npm but installs Veltrix, a Windows RAT that steals browser credentials, Discord tokens, and keystrokes via a hardcoded Discord webhook.
Malicious Pull Requests: A Threat Model
A compact threat model of the malicious pull request as a supply chain attack primitive against GitHub Actions: attacker, goals, assets, controllable surface, and an attack vector taxonomy (V1...
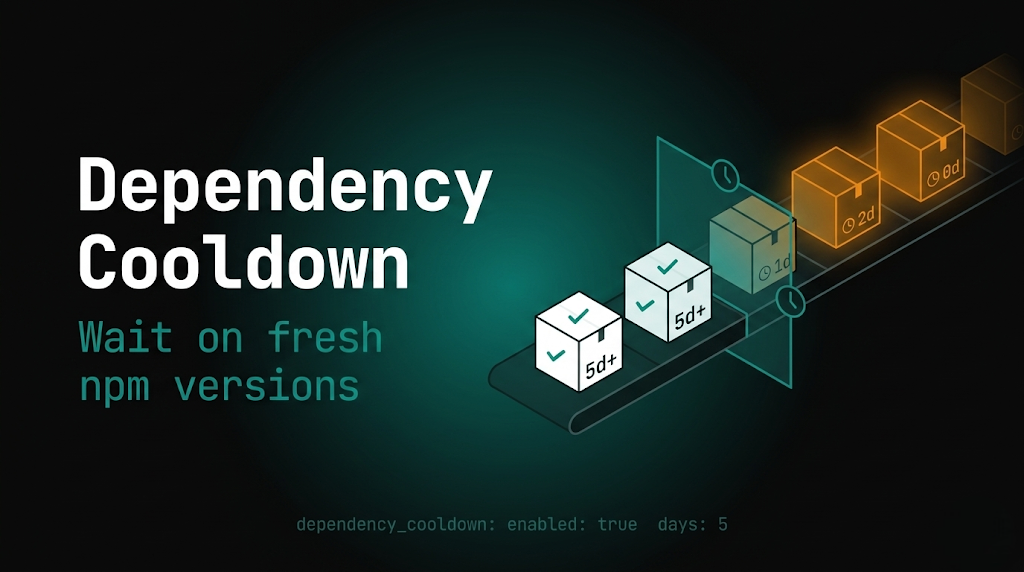
PMG dependency cooldown: wait on fresh npm versions
Package Manager Guard (PMG) blocks malicious installs and now supports dependency cooldown, a configurable window that hides brand-new npm versions during resolution so installs prefer older,...
Ship Code.
Not Malware.
Start free with open source tools on your machine. Scale to a unified platform for your organization.
